In March 2018, the State Higher Education Executive Officers Association (SHEEO) held a Community of Practice convening, “Integrating Independent Institutions in Postsecondary Data Systems,” in Denver, Colorado. Part of a larger project funded by the Bill & Melinda Gates Foundation, the March meeting included participants from nine states, representing independent institutions and state data systems, to discuss the capacity and effective use of state postsecondary data systems and best practices for integrating independent institutions into such systems. One of the focus areas was to discuss broad concepts related to security, privacy, and data governance in postsecondary data systems and to identify the security, privacy, and data governance concerns inherent in integrating independent institutions in such systems, and suggest potential ways to resolve those concerns. Meeting participants participated in a workshop to help unpack some of these issues.
Speaking the Same Language
Participants acknowledged that one of the difficulties in addressing data governance, security, and privacy issues is that business owners and researchers may not be using the words data governance, security, and privacy in the same way that information security practitioners use those words. As part of a level-setting exercise, participants used a live polling tool to evaluate the IT definitions of these terms against their own experiences:
- Data Governance: Executive management’s responsibility to provide strategic direction, oversight, and accountability for an organization’s use of information and information systems.
- Information Security: The study and practice of protecting information. The main goal of information security is to protect the confidentiality, integrity, and availability of information.
- Privacy: A person’s right to have control of his or her own personal data. The person has the right to specify how that identifiable data is collected, used, and shared.
For example, a little over half the participants in the room (55 percent) weren’t sure if the IT definition of data governance matched their own experiences, although most participants in the room were confident that data governance activities did need to include processes and procedures for accessing data for research and operational purposes. While talking about information security concepts, members of the audience reported that confidentiality (41 percent) was the most important information security concept in questions regarding participation in state data systems.
Identifying the Issues
Workshop participants brainstormed on the most important data governance, security, and privacy issues inherent in how independent institutions participate in postsecondary data systems.
The identified issues included:
- How can we build in safeguards so that private institutions feel that their data, when contributed to state data systems, is secure, private, and the institution is protected from liability considerations?
- Why are there not more similarities among the states in how they address data governance, security, and privacy issues?
- Are there standard data elements that all states could agree on regarding data governance that would make participation more attractive to independent institutions?
- Who should be the decision maker for data governance issues, the IT department or the business stakeholders?
- How do states handle public information requests and are there any circumstances in which you would re-identify data?
- How do you know your data is secure?
- Who has access to what information?
- How do we determine what is private and what is not?
- How do we protect the privacy of our students in a longitudinal system; can we be sure they will not be re-identified or identifiable? How is data shared in response to research requests?
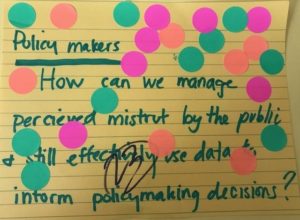
- How do we address perceived mistrust by the public and still effectively use data to inform policymaking decisions?
- Do students (and parents in some instances) trust institutions and state data systems with this data? Do they understand what the data are being used for?
- Are opt-outs reasonable when independent institution reporting is not legally required; what do they do to the data set?
- How do we provide context about our institutional programs when the data are shared for decision-making purposes?
From this list, meeting participants voted (see image below for the top-rated issue receiving votes from 24 of the 30 attendees) on the issues to identify three overarching issues of importance: (1) how to address perceived mistrust by the public and still effectively use data to inform policy-making decisions; (2) whether a set of data governance standards could be created and shared among the states as best practices; and (3) who has access to the data contained in state data systems?
Building Trust
During the discussion on these top three issues, one theme emerged: the importance of trust. This trust was enumerated in many different ways:
- Trust between the student (and parent in some circumstances) and institution that providing data to the state data system is important and necessary; that data will be protected.
- Trust between the independent institution and the state, to ensure that data will be protected and used in only the ways contemplated by signed data-sharing agreements.
- Trust between the independent institutions, the state, and policymakers, that statistics provided by state data systems will be used in transparent ways with an institutional opportunity to provide context to any statistics that are shared.
Possible projects moving forward could include a model system of data governance or suggested model data-governance terms regarding how independent institutions can participate in state data systems; participation principles for independent institutions; or a model code of privacy conduct that both independent institutions and state data systems can refer to when questions of data access and reporting arise.
The sine qua non of postsecondary data system collection efforts is the ability to use, share, and rely upon (e.g., trust) the data included in such efforts. Without the ability to effectively use the data, no one institution or entity can meet its goals. And our community’s shared goals, particularly the critical goals focused on student success, outcomes, and accessibility, will be challenging to realize. The implementation of information security and privacy practices and good data governance processes can go a long way toward establishing the trust needed in the postsecondary data system ecosystem.
Lisa Gesner is Content Manager, Marketing for EDUCAUSE. Joanna Lyn Grama is Senior Consultant at Vantage Technology Consulting Group.
